Managed Detection & Response Service
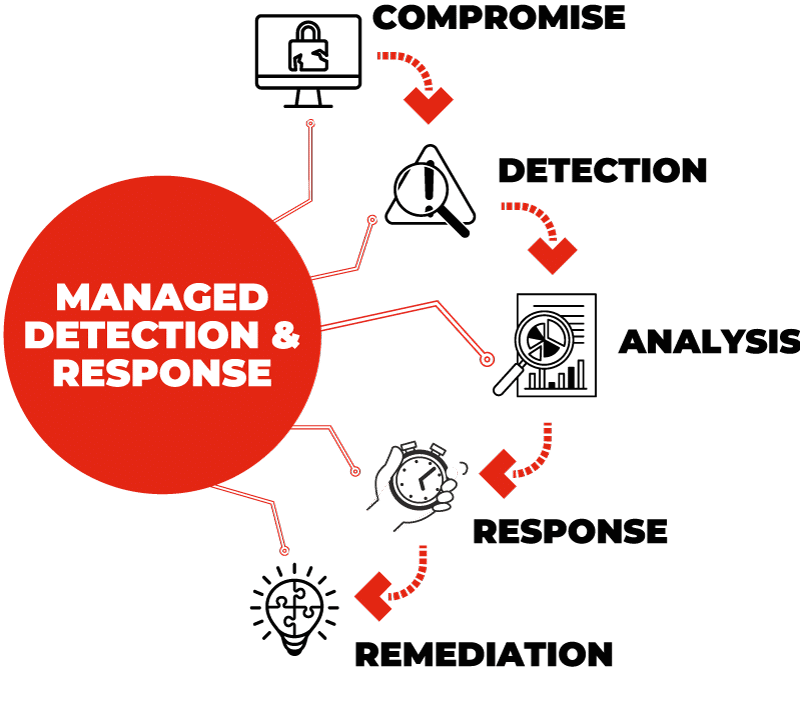
Organisations across the globe will have Antivirus software in place already as part of their cyber security strategy. Sole reliance on this can result in a false sense of security, leaving your organisation vulnerable. This means it is no longer adequate to fully protect and defend in an increasingly sophisticated landscape of cyber threats. This is where Acora’s modern Managed Detection and Response (MDR) Service comes in, providing 24/7/365 support to manage your security environment.
The Acora MDR cyber security service assists organisations in detecting, responding to, and mitigating cyber threats by combining advanced technology, human expertise, and proactive threat hunting. Delivering a customised cyber security program to your business, we take on a personal approach to handling security alerts, making decisions and sending you regular reports to keep you fully informed about what is going on in your environment.
The right level of protection across your business
Most Security and IT professionals will already have Endpoint, Detection and Response (EDR) capabilities in place that focus solely on endpoint protection. However, we know that organisations urgently need to extend their current capabilities to get more protection for the same cost. In addition to this, current services are not set up to support incident response, relying on automated alerts rather than human expertise.
Partnering with Gartner leader SentinelOne, Acora’s MDR Service combines market-leading technology and experience all under one 24/7 Managed Service.
Acora’s MDR Service Benefits
- Benchmarked against Gartner's Magic Quadrant and the Mitre Att&ck Framework
- Providing Security and IT professionals with the ability to access enterprise-grade security tools
- Supports incident response and advisory with human expertise instead of automated alerts
- Managed by one relationship and one platform, taking full accountability
MDR vs EDR
Endpoint Detection and Response (EDR) is an integrated security system focusing on endpoint security. The system combines real-time continuous monitoring and collection of endpoint data with rules-based automated response and analysis capabilities. It detects, investigates and responds to suspicious activities on hosts and enables security teams to identify and respond to threats quickly.
Acora’s MDR Service enhances an organisation’s threat detection, analysis, and response capabilities far beyond EDR. By combining advanced technology, human expertise, and proactive threat hunting, MDR assists organisations in detecting, responding to, and mitigating cyber threats. As an effective MDR provider, we have 24/7 Security Operation Centres (SOCs), Incident Response Teams, and the ability to secure various platforms.
Acora’s MDR Service Capabilities
Broader Security: MDR goes further than endpoint protection, providing network-wide visibility and protection, filling any security gaps across the entire IT environment.
Access to Cyber Security Experts: By outsourcing the service, organisations are given access to a team of skilled cyber security professionals. This reduces the need to attract, train and retain internal team members, freeing up time to concentrate on core business operations.
24/7 Monitoring and Rapid Response: Our MDR Service round-the-clock monitoring ensures that potential threats are identified promptly and swiftly responded to, limiting their impact and scope.
A holistic approach to endpoint security
At Acora, we have integrated our award-winning Managed SOC to create a comprehensive, fully Managed MDR Service, providing clients with cost-effective, continual and in-depth cyber protection. Flexible and scalable, the Acora MDR Service can be tailored and customised to support your business requirements.
Recognised as one of the top 10 managed service providers globally and with ISO Accreditations for Security, Quality, Service Management & Business Continuity, we are paving the way with our Experience Led Approach™. Our processes and procedures are monitored to the highest industry standards and our SOC team are highly trained, giving you access to a trusted team of experienced cyber security experts.
Acora is challenging the status quo, bringing together the best technology and user experience to our customers.
Acora’s MDR Service Fundamentals
- Threat Detected: Our detection engines identify the threat and perform initial mitigation actions.
- Analyst Deep Dive: Acora Analysts investigate each threat, leveraging rich endpoint telemetry, threat intelligence, and other threat details.
- Threat Insights: All threats are annotated with analyst findings to keep you in the loop.
- Action and Next Steps: Threats are automatically mitigated and resolved. Threats are escalated only when necessary.
- Advanced MDR Functions: Forensic deep dives, targeted threat hunting and incident response can be triggered manually.