-

FORTINAC
NETWORK ACCESS CONTROL SECURITY FOR NETWORKS WITH IOT
PROTECT NETWORKS WITH IOT DEPLOYMENTS
With the proliferation of IoT devices, it is crucial that organisations can identify and profile the various endpoints connecting to their networks. A Network Policy and Access Control solution can profile those devices and then assign these appropriate levels of access and segmentation for preventative containment.
With continuous monitoring of the network, our solution can detect endpoint risks and automatically orchestrate a response by Fortinet and 3rd party devices.
Visibility and Control
FortiNAC is a network access control solution that further enhances the Fortinet Security Fabric.
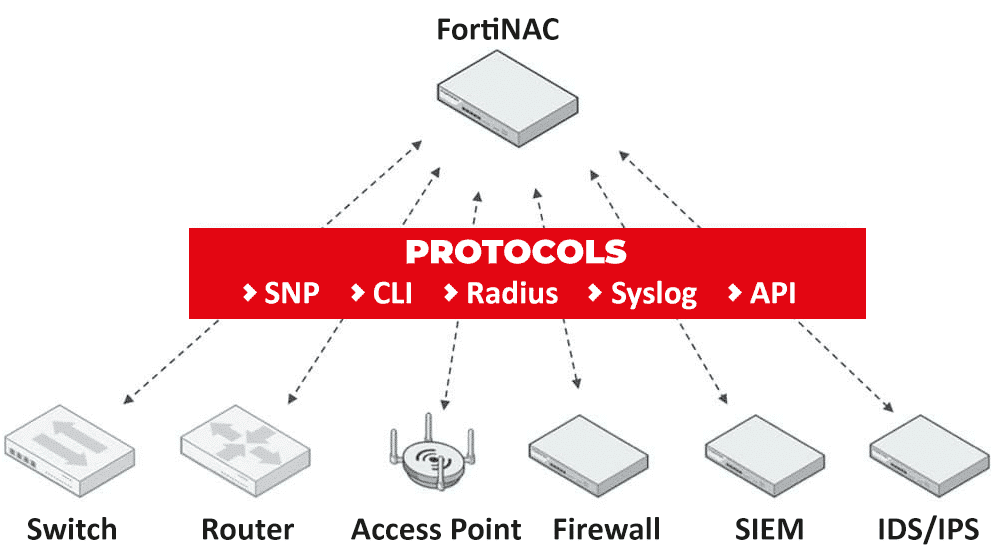
Providing advanced protection against IoT threats, FortiNAC extends control to third-party devices, and orchestrates automatic responses to a wide range of networking events.
FortiNAC is an ‘out of band’ solution, meaning it does not sit in-line of user traffic. This architecture allows FortiNAC to be deployed centrally and manage many remote locations. Visibility, control, and response are achieved by integrating with, and leveraging the capabilities of, the network infrastructure.
Key FortiNAC Features
- Identify and profile every single trusted and untrusted device
- Automate the threat response for Fortinet and 3rd party network devices
- FortiNAC can be deployed centrally and manage remote locations
FortiNAC Protects
Due to an increase of BYOD (bring your own devices) and SMART devices connecting to networks, corporate infrastructures are growing in complexity, bringing substantial new security risks as unsecured devices dramatically increase the risk of intrusion, breach, and a catastrophic cyberattack.
Network Access Control (NAC) solutions ensure compliance for all devices connecting to networks, checking that proper controls are in place before corporate network resources are accessible.
FORTINAC CAN BE DEPLOYED CENTRALLY AND MANAGE REMOTE LOCATIONS
We have invested significantly in training our security consultants to become experts in the complete portfolio of Fortinet security products and solutions.
Our highly trained team can be trusted to design, operate and manage comprehensive security solutions for even the most complex of environments.
As a Fortinet partner of distinction, we are extremely proud to provide our clients the highest level of cyber security protection, service and support.
FORTINAC BENEFITS
- Agentless scanning: Detect and identify headless devices as they connect to the network analytics
- 17 profiling methods: Utilise up to 17 different ways of determining the identity of a device
- Simplified onboarding: Automate onboarding process for large number of endpoints, users, and guests
- Micro-segmentation: With identified devices, FortiNAC can narrowly restrict network access for those devices to only necessary network assets
- Extensive multi-vendor support Interact with and configure network devices (switches, wireless access points, firewalls, clients) from more than 150 vendors
- Scalability: FortiNAC architecture enables effective scaling to multi-site locations and supporting millions of devices
- Fortinet Security Fabric: FortiNAC can be deployed either as a standalone device or as part of the Fortinet Security Fabric
Network Policy & Access Control
The IoT revolution has raised a new challenge for network owners. How can you see and protect against a myriad of devices showing up on the network? Network Access Control has come back to the forefront of security solutions to address that challenge. This technology was deployed to assist with bring-your-own-device (BYOD) policies and is now getting renewed focus as a means to safely accommodate headless IoT devices in the network.
The FortNAC solution protects both wireless and wired networks with a centralised architecture that enables distributed deployments with automated responsiveness.
FortiNAC enables three key capabilities to secure IoT devices:
Collectively, the following three capabilities provide the tools that network owners need to secure a world that is embracing IoT.
- Network visibility to see every device and user as they join the network
- Network control to limit where devices can go on the network
- Automated response to speed the reaction time to events from days to seconds
FortiNAC Resources
Focusing on network security and operational security technology, explore a number of key FortiNAC resources that address key challenges for many Cyber Security leaders.
-

Data Sheet: Security for Networks with IoT
-

Role-based Dynamic Network Access Control
-

Ensuring Operational Technology Security
-

FortiNAC Simplifies Comprehensive IoT Security
Get in Touch
To speak to one of our trusted advisors about the FortiNAC Network Access Control Solution, please leave a few contact details and our team will be in touch.
Or feel free to give us a call and speak with someone immediately.